In this exploration, delve into the intricacies of innovative technological blueprints, where precision meets prowess. Unveil the essence of state-of-the-art documentation, revealing the intricacies of modern engineering marvels. Embark on a journey through the intricate labyrinth of technical insights, where every detail serves as a cornerstone in the architecture of advancement.
Discover the intricately woven fabric of technological prowess, where each strand contributes to the tapestry of innovation. Delve into the core of technical blueprints, where clarity reigns supreme and complexity finds its elegant resolution. Navigate through the labyrinth of specifications, where every twist and turn reveals a new facet of ingenuity.
Join the expedition into the realm of technical intricacies, where the language of innovation speaks volumes beyond mere words. Unravel the enigma of cutting-edge documentation, where each page holds the promise of unlocking new dimensions in understanding. Embark on this odyssey of discovery, where the journey is as enlightening as the destination.
Unlocking the Potential of 5220 Palo Alto Datasheet

Delving into the intricacies of the comprehensive dossier detailing the 5220 Palo Alto system opens pathways to harness its full capabilities. Within these pages lie the keys to maximizing efficiency, enhancing security, and optimizing network performance.
Embark on a journey of discovery as we decode the nuances encapsulated within this extensive compendium. Unveil the array of features, functionalities, and innovations meticulously crafted to elevate operational prowess and fortify digital landscapes.
Explore the depths of insight woven into the fabric of this document, transcending mere data points to unveil a roadmap towards strategic empowerment. Unlock the treasure trove of knowledge and leverage it to navigate the ever-evolving terrain of network architecture with confidence and finesse.
Understanding Key Features and Specifications
In this section, we delve into the essential aspects and technical details that characterize the 5220 Palo Alto device. By exploring its core functionalities and performance metrics, we aim to provide a comprehensive understanding of its capabilities and potential benefits.
Performance Metrics: The device’s operational efficiency and effectiveness are measured through a series of performance metrics. These metrics encompass factors such as throughput, latency, and scalability, offering insights into its responsiveness and ability to handle varying workloads.
Security Protocols: A fundamental aspect of the device lies in its robust security protocols. These protocols encompass a range of features, including encryption standards, intrusion detection mechanisms, and threat prevention capabilities, ensuring the integrity and confidentiality of data transmission.
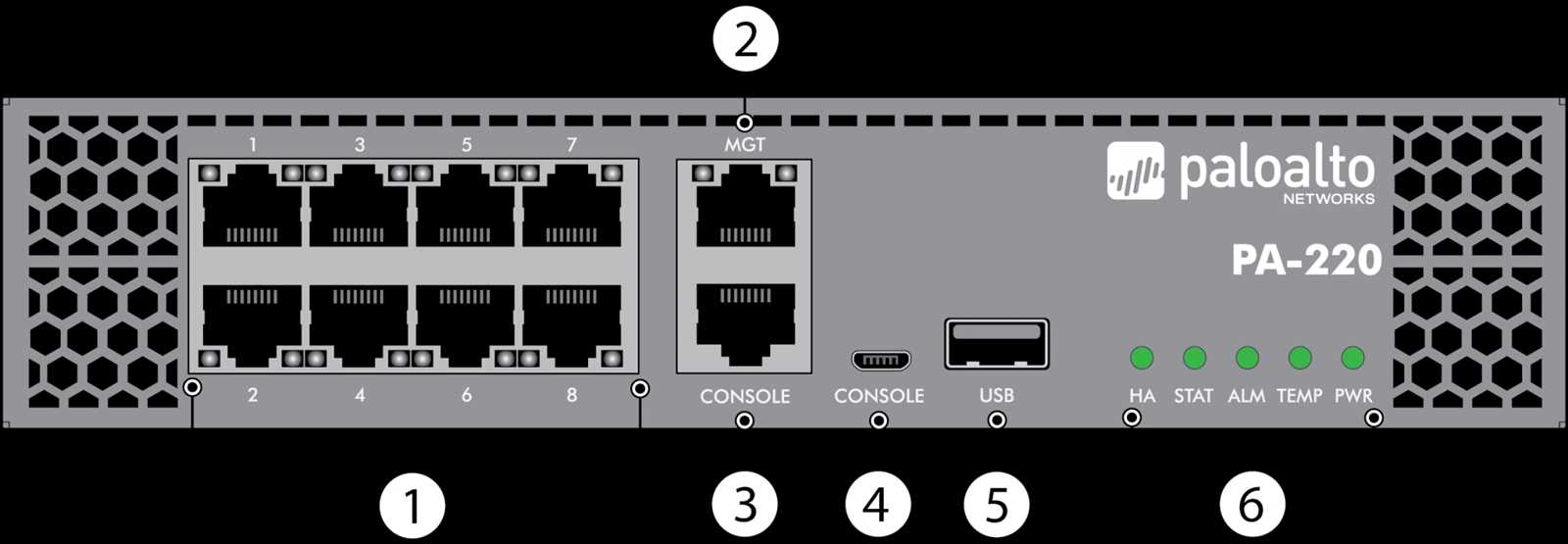
Scalability and Flexibility: The device’s scalability and flexibility are vital considerations for adapting to evolving network requirements. By examining its scalability features, such as the number of supported connections and expandable storage options, alongside its flexibility in deployment scenarios, organizations can assess its suitability for diverse environments.
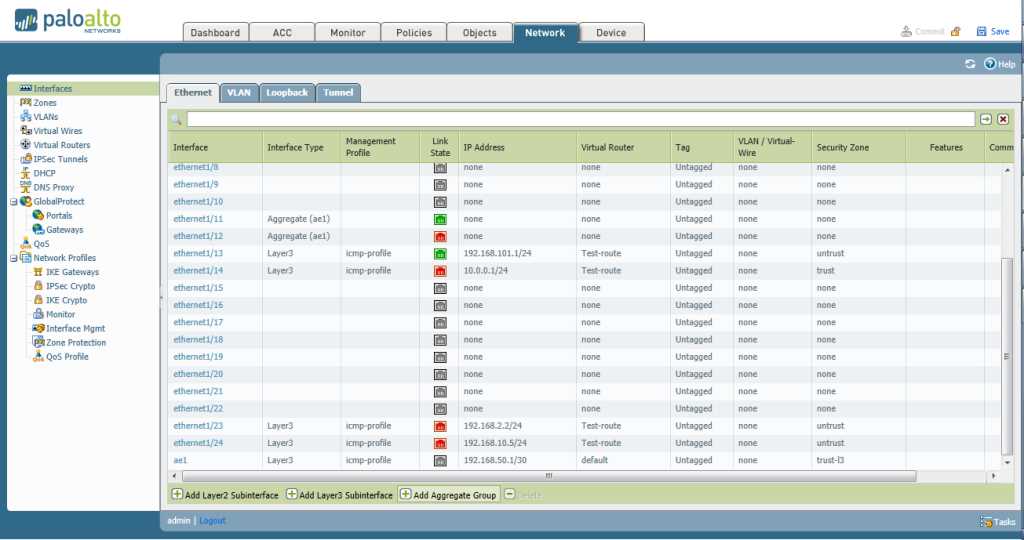
Management and Monitoring: Effective management and monitoring capabilities are integral to maintaining optimal performance and security posture. Through centralized management interfaces, intuitive dashboards, and real-time monitoring tools, administrators can efficiently oversee and troubleshoot network operations.
Integration and Compatibility: Seamless integration with existing infrastructure and compatibility with industry-standard protocols are key facilitators of interoperability. By ensuring compatibility with common networking protocols and offering integration options with third-party applications, the device enhances operational efficiency and facilitates streamlined workflows.
Reliability and Redundancy: Reliability and redundancy mechanisms are essential for minimizing downtime and ensuring continuous operation. Through features such as failover protection, high availability configurations, and redundant hardware components, the device mitigates the risk of disruptions and safeguards business continuity.
Optimization and Performance Tuning: Fine-tuning performance parameters and optimization strategies are crucial for maximizing the device’s efficiency. By leveraging optimization techniques such as Quality of Service (QoS) controls, load balancing algorithms, and traffic prioritization mechanisms, organizations can optimize resource utilization and enhance overall network performance.
Compliance and Regulatory Standards: Adherence to compliance regulations and industry standards is paramount for maintaining legal and regulatory compliance. By complying with standards such as GDPR, HIPAA, and PCI DSS, and offering features to support regulatory requirements, the device facilitates adherence to data protection and privacy mandates.
By comprehensively understanding these key features and specifications, organizations can make informed decisions regarding the adoption and integration of the 5220 Palo Alto device within their network infrastructure.
Optimizing Network Security with 5220 Palo Alto
In this section, we delve into enhancing network security through the utilization of cutting-edge solutions provided by the innovative 5220 Palo Alto system. By leveraging advanced technologies and robust features, organizations can fortify their digital infrastructure against a myriad of threats, ensuring comprehensive protection and peace of mind.
- Maximizing Firewall Efficiency: Explore methods to bolster firewall performance and streamline operations, augmenting the defense mechanism against cyber intrusions and unauthorized access attempts.
- Enhancing Threat Detection Capabilities: Implement strategies to elevate threat detection proficiency, enabling timely identification and mitigation of diverse cyber threats, ranging from malware infiltration to sophisticated cyber attacks.
- Strengthening Access Control Measures: Delve into techniques for enhancing access control protocols, empowering organizations to regulate network access with precision and granularity, thereby minimizing the risk of unauthorized entry and data breaches.
- Optimizing Intrusion Prevention Strategies: Examine approaches to optimize intrusion prevention methodologies, fortifying network perimeters against intrusion attempts and proactively thwarting malicious activities before they escalate into significant security incidents.
- Ensuring Secure Data Transmission: Explore methodologies to ensure the secure transmission of sensitive data across networks, leveraging encryption protocols and secure communication channels to safeguard information integrity and confidentiality.
By implementing these proactive measures and harnessing the capabilities of the 5220 Palo Alto system, organizations can achieve a resilient network infrastructure capable of withstanding evolving cyber threats and safeguarding critical assets against potential compromises.
Integration and Deployment Strategies for 5220 Palo Alto
In this section, we delve into the seamless amalgamation and rollout tactics tailored for the 5220 Palo Alto infrastructure solution. Our focus lies on the orchestration and implementation methodologies conducive to harmonizing the 5220 Palo Alto system within existing frameworks and operational environments. We explore strategies for the convergence of diverse systems, fostering cohesion and interoperability.
Deploying the 5220 Palo Alto entails a meticulous choreography of components, necessitating astute planning and resource allocation. Emphasis is placed on the orchestration of disparate elements, fostering synergy without compromising on operational integrity. This involves a strategic interplay of configurations, protocols, and interfaces, aligning the deployment with organizational objectives and operational imperatives.
Integration of the 5220 Palo Alto transcends mere technical amalgamation; it embodies a holistic approach towards unifying disparate infrastructures. Through cohesive integration frameworks, we endeavor to transcend siloed paradigms, fostering a unified ecosystem conducive to streamlined operations and enhanced security postures. Leveraging best practices and tailored integration patterns, we navigate the intricacies of integration with dexterity and finesse.
Furthermore, our discourse extends to the dynamic landscape of deployment strategies, encompassing phased rollouts and iterative approaches. By delineating deployment lifecycles and provisioning mechanisms, we pave the way for a systematic and controlled deployment of the 5220 Palo Alto solution. This iterative approach fosters adaptability and resilience, mitigating risks while maximizing operational efficacy.
In summary, the integration and deployment strategies for the 5220 Palo Alto solution encapsulate a comprehensive approach towards harmonizing diverse systems and orchestrating seamless deployments. Through meticulous planning, strategic alignment, and iterative refinement, we navigate the complexities of integration and deployment with precision and acumen.